In recent days, there has been growing attention around Anthropic and its project Glasswing, which aims to bring AI closer to both offensive and defensive cybersecurity. The hype is understandable: tools capable of analyzing complex vulnerabilities and simulating advanced attacks represent a meaningful shift.
However, while the spotlight is focused on a few major players and on technologies with limited access, there are also practical implementations already demonstrating similar capabilities—often with far less visibility. In this context, we applied our technology to a real-world scenario to evaluate its effectiveness.
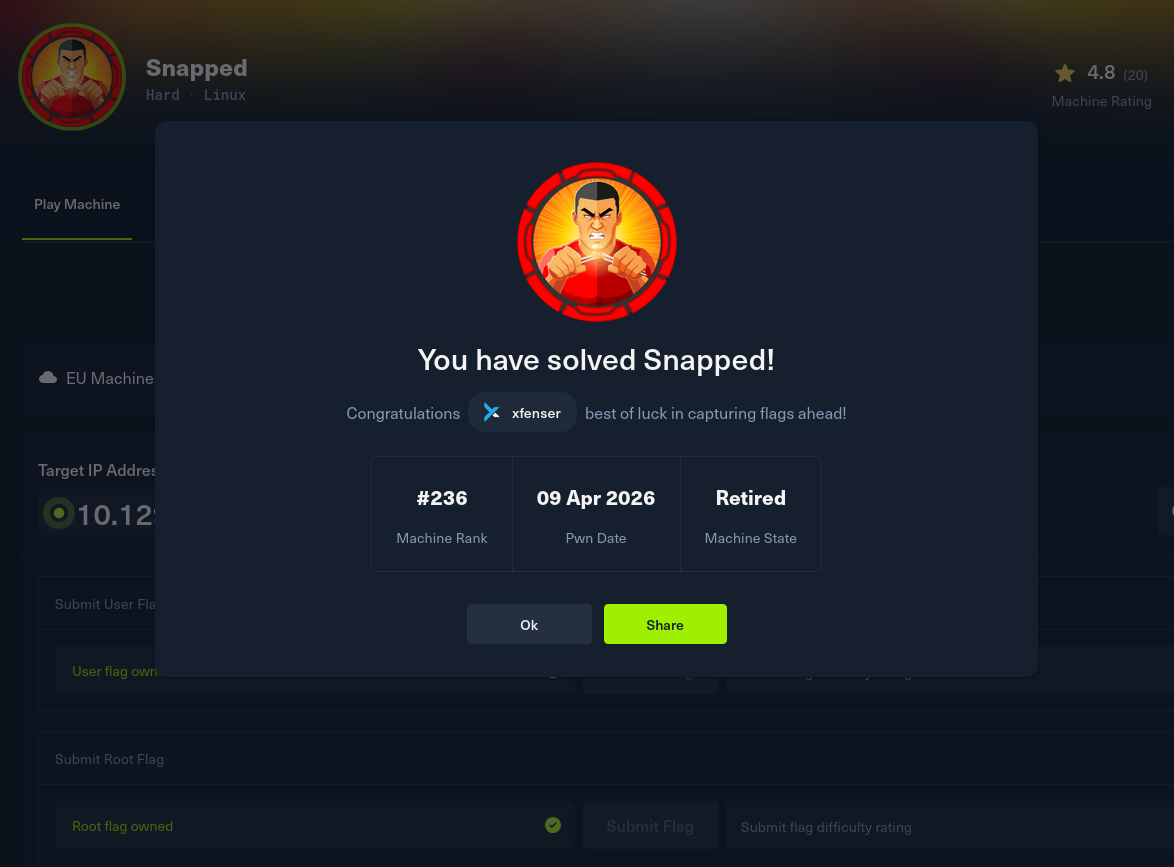
A Real Test: Hack The Box “Snapped”
To assess its capabilities, we used a machine from Hack The Box called “Snapped,” classified as hard difficulty. The scenario is far from trivial: an attack chain combining two recent and technically sophisticated vulnerabilities.
The most relevant outcome is not the compromise itself—expected in a CTF environment—but the fact that the entire operation was executed fully autonomously, without human intervention.
From Surface to Foothold
The initial phase leverages CVE-2026-27944, a flaw in Nginx-UI exposing a backup endpoint without authentication.
Our technology was able to:
- automatically identify exposed services (SSH and HTTP)
- detect the vulnerable Nginx-UI instance
- retrieve the full configuration backup via
/api/backup - extract the encryption key from HTTP headers
- decrypt the data and recover credentials
This stage, often underestimated, requires a combination of enumeration, contextual understanding, and data processing.
Privilege Escalation: A Non-Trivial Race Condition
After gaining user access, the second phase involved CVE-2026-3888, a TOCTOU vulnerability in snap-confine.
Here, the technical complexity increases significantly:
- synchronization with
systemd-tmpfiles - exploitation of a race condition on temporary directories
- manipulation of the bind-mount process
- dynamic linker hijacking on SUID binaries
This type of exploit chain typically requires an experienced operator. In this case, it was executed autonomously up to full root compromise.
Why This Matters
Comparisons with tools like Glasswing are natural, but the point is not to establish hierarchy. Instead, this highlights a broader trend:
- attack automation is becoming practical
- complex exploitation paths can be handled end-to-end
- meaningful results are not limited to highly funded or restricted-access systems
This experiment shows that autonomous systems can already operate across real, multi-step attack chains with significant technical depth.
A Pragmatic Perspective
The current wave of attention is useful—it brings focus to an important space. At the same time, some of the most relevant progress is happening through concrete experimentation.
The “Snapped” case does not just demonstrate feasibility—it shows that autonomous exploitation is already operational in realistic scenarios.